If you’ve been long enough in the crypto sphere you’ve probably heard of Bismuth from your crypto friends or the so called “crypto-twitter celebrities” hyping up the project.
Bismuth is claiming to be the first Python based blockchain focused on providing an ecosystem for developers in order to build unique dApps. Unlike most altcoins, Bismuth was built from top to bottom without forking or copying any of the other coin’s code – starting from the protocol level and ending by its contemporary conception.
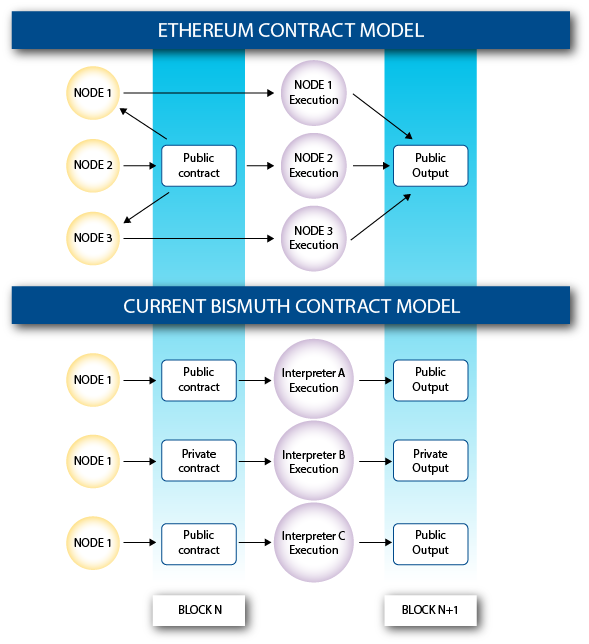
This is really important to know before continuing the Hypernodes part. Let me provide you a schema to imagine how the Bismuth model is actually working:
About Hypernodes:
A hypernode is a type of masternode, which doesn’t operate on the same blockchain.
When It comes to Bismuth, there are two blockchains. The main one uses Proof-of-Work (PoW) consensus algorithm to keep the network alive and secure. There’s also a second one which uses the Proof-of-Stake (PoS) concept. This PoS chain is directly connected to the main one to decrease the chances of attacking the primal PoW chain.
How does this happen?
Let’s think of these hypernodes as watchers or guardians. They observe the main chain’s consensus rules but also check the PoS chain for good and bad performants. Each hypernode on the network is evaluating using a KPI (Key performance indicator) so the ones who perform bad will get kicked out of the Hypernode-circle.
Since there are two chains directly connected with each other, you might be wondering why is it harder to “attack” it when compared to traditional blockchains?
Let’s imagine a 51% attack on the Bismuth’s network. What happens ?
Since most of the hash power is controlled by one person (1 pool most of the time), he can refuse transactions or change the consensus, but since we have hypernodes watching over the network, they are able to stop the attacker from making any drastic changes.
Since it is a separate chain, the PoW can’t change the consensus of the PoS one. Even if the attacker has 80 % of the hash power, this won’t change the PoS ledgers and everything will get back to normal. Consider it as a double-ledger network, where each chain has it’s own up to date ledger and it’s own metrics.
What happens when Hypernodes detect an attack on the PoW chain?
They simply ban the intruder for a certain period of time. The punishment increases every time the impostor attempts to manipulate the network.
Does this mean that the hash power drops and the speed of the network falls down?
Not really. The difficulty readjustment occurs every single block. So even if the hash power of the network drops with 80 %, the power will be calculated and adjust accordingly.
Here’s a quotation from one of the team members when asked about possible attacks on the network:
“Every attack will make the network stronger by helping to identify the right metrics and suspicious activities. In the worst case scenario, we would have unmatched data at hand to retrace and help fix future issues. Some attacks on the Bismuth network are currently undergoing, were conducted before, and those metrics collection show them very clearly. (and the network does a pretty good job coping with them) So there is no doubt the HN will make any cheat attempt both harder to be effective, and almost impossible to go unnoticed.“ – SySy (Discord)
So does that make the network “unhackable” ?
This is a common misconception about software in general. There is no such thing as “unhackable” program, but at least it makes it very secure.
A person can still manipulate it if he or she has up to 51% of the PoW hash power and control over 60 % of the hypernodes.
Requirements for running a hypernode:
Hardware requirements:
- Linux OS (VPS or Dedicated server)
- Static IPv4 address
- 10 GB disk space (preferably SSD)
- 4 GB of RAM memory
- 2 CPU cores (GHz not announced yet)
- Unmetered bandwidth is preferable.
Now, when you’re aware of the hardware requirements, let’s talk about how many coins you need to lock up as collateral.
You can either chose between 10,000 BIS , 20,000 BIS or 30,000 BIS.
Why there’s such a difference between the amounts?
They’ve decided to give investors the option to choose between these three collateral levels. There’s no difference if you’re going to set up three Hypernodes with 10,000 each of it or one Hypernode with 30,000 as a collateral. The one that costs 30,000 has the same weight on the network as 3 Hypernodes with 10,000 BIS collateral each.
What about the reward?
Same story. If you lock in 30,000 BIS Hypernode, you will receive the reward of the 10,000 BIS Hypernode multiplied by three. Financially speaking it doesn’t matter which one you would set up.
Anyway, there are two reasons to use a 30,000 BIS Hypernode:
- Maintenance – You need to upgrade your hypernode only once instead of logging in to each of them.
- Cheaper – You will save money on VPS services. Instead of paying $20 for each VPS ($60) you can only purchase 1 VPS ($20).
Can I lock in different amounts ?
Unfortunately, no. You can choose between 10,000 / 20,000 / 30,000 BIS collateral.The team is considering the implementation of “Shared Hypernodes” but it’s still a concept.
Maintenance:
You’ll need to upgrade the Hypernodes separately from the PoW full nodes, because they use different chains. So, you’ll have to frequently check their twitter page for updates (Preferably every morning).